Before defcon, I decided to set up a VPN for my internet traffic. I could not find any good VPN offerings for my needs, as they are all geared towards people doing sketchy things and not wanting to be tracked, or people overseas wanting access to sites that are blocked in their current locations. Most charge monthly fees and most are sketchy.
Amazon EC2 gives you one year free to host a system in their cloud. I run my server off the default Amazon Linux AMI (Amazon Machine Image) which is based on Redhat. I mostly followed the directions at: Setting up OpenVPN on Amazon’s EC2.
Amazon EC2 OpenVPN Configuration
- Run the following on the server:
yum install openvpn
openvpn —genkey —secret /etc/openvpn/openvpn-key.txt
- Create a file `/etc/openvpn/openvpn.conf` with contents:
port 1194
proto udp
dev tun
secret openvpn-key.txt
# The server's virtual endpoints
ifconfig 10.8.0.1 10.8.0.2
push "redirect-gateway def1"
keepalive 10 120
comp-lzo
persist-key
persist-tun
status server-tcp.log
verb 3
- Run the vpn:
service openvpn restart
chkconfig openvpn on
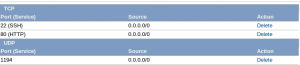
- Open up the firewall
- Get iptables to route your traffic:
iptables -A INPUT -i tun+ -j ACCEPT
iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERADE
OSX Client system Configuration
- Install tunnelblick.
- Copy the key file created previously to the config directory:
cd ~user/Library/Application\ Support/Tunnelblick/Configurations/
cp /tmp/openvpn-key.txt .
- Create config file:
dev tun
proto udp
port 1194
remote server_address.com
resolv-retry infinite
nobind
secret openvpn-key.txt
ifconfig 10.8.0.2 10.8.0.1
comp-lzo
verb 8
redirect gateway def1
You can also use viscosity as opposed to Tunnelblick, but it costs money. However, it is free for the first 30 days and it's error messages are more helpful if you have problems.
Everything should now be working, so go to a site that checks your IP from the OSX system and ensure it has changed. May also want to run tcpdump to ensure all traffic is going to the EC2 IP.